DNS Filtering
Japanese English
Revised at 2019/06/17 about notes for DNS filtering function. (Add the link)
overview
Cyber-attacks that target the individual such as spoofed emails (*1) and forms of malware like ransomware (*2) continue to increase year after year.
In the Internet environment of today, computers, smartphones, IoT devices and all other devices that use the Internet are potential targets of cyber-attacks, or potential relay points for such attacks.
Internet Initiative Japan Inc. (IIJ), the provider of IIJmio, has taken countermeasures against such attacks, and is regularly examining various other initiatives to ensure safe and secure use of the Internet by its users.
In light of this state of society, IIJ will implement malware countermeasures using DNS filtering on the Internet connection services that it provides.
![]() https://www.iij.ad.jp/sec-statement/
https://www.iij.ad.jp/sec-statement/
Function for Malware Countermeasures Using DNS Filtering
When devices using lines provided by IIJmio become infected with malware and attempt to communicate with C&C servers (*4), etc., this function automatically detects that attempt and said communication is blocked by the DNS server (*5).
These countermeasures make it possible to mitigate the risk of leaks of personal information and other accidents caused by malware infections.
※ Communications other than those made to servers recognized as C&C servers by IIJ can be made normally.
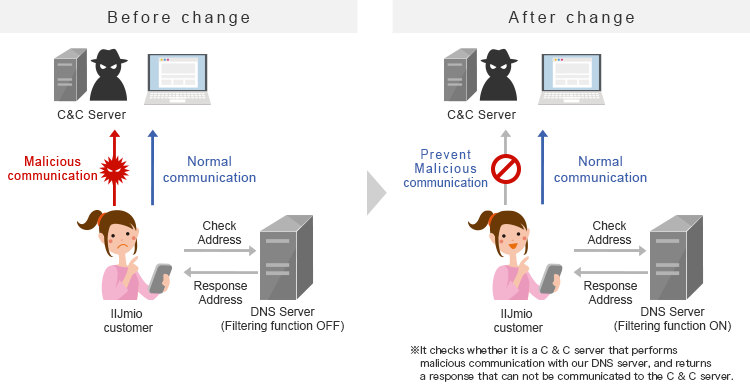
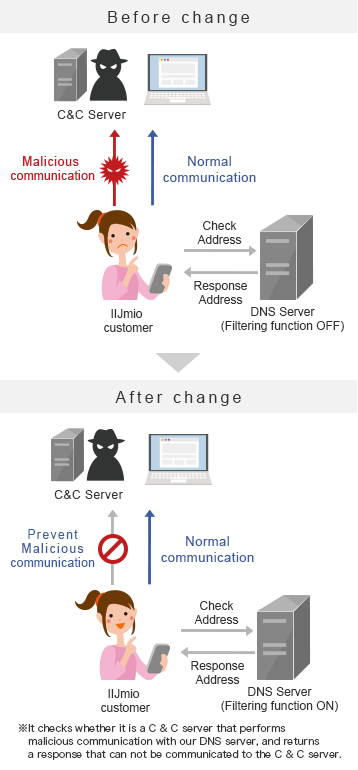
※ simplified illustration for focusing on easy-to-understand
Start Date
- 2019/7/1(Mon.)
Applicable services
- IIJmio Mobile Service
- IIJmio Mobile Plus Service
- IIJmio eSIM Service
- IIJmio IoT Service
- IIJmio Prepaid Pack
- Japan Travel SIM
- Japan Travel SIM for Unlocked Phone
- IIJmio Hikari
- IIJmio FiberAccess/NF
- IIJmio FiberAccess/DF
- IIJmio FiberAccess/SF
How to perform settings
No new procedures need to be carried out.
The function will be automatically enabled for all users currently using the above applicable services.
How to modify settings for DNS filtering function
IIJ recommends that users use this function. However, users who do not wish to do so may disable it at any time for each individual line.
No charges will be incurred by disabling or enabling the function.
For details, please see the below page.
![]() FAQ
FAQ
Important matters to note
- This function does not prevent your computer or smartphone from becoming infected with malware.
- It is necessary that you take measures on your own to exterminate malware, prevent infection from it, etc. for the computers and smartphones that you use.
- IIJ cannot be held liable for any damage that occurs as a result of malware infections, nor can it investigate the causes of such infections.
- The blocking of communications to C&C servers is conducted for each individual line that you have an agreement with IIJ for.
- Communications to C&C servers are mechanically detected and blocked through analyses of query logs for DNS servers conducted on an information analysis platform at IIJ. IIJ cannot disclose details of that process, including block frequency and dates and times blocked.
- Please note in advance that this function does not constitute a guarantee that all malicious communications can be blocked.
- If you have any further question, please see the link below.
Email by a malicious third party spoofing a specific individual (or corporation)
(*2) ransomeware
Malware that illegally rewrites data saved on a computer and demands money as compensation for restoring that computer
(*3) malware
General name given to software that causes harm, such as computer viruses and worms
(*4) command and control server
Computers and other devices installed for the purpose of remotely controlling malware *"bots" (a type of malware) engage in activities such as extracting data from infected computers in accordance with the orders of a C&C server.
(*5) DNS server
Computer or other device with a mechanism for managing the correspondence between URLs and IP addresses
*In order to access a website over the Internet, an "IP address," which can be likened to a computer's address, is needed. When accessing a website using an URL (a string of characters such as "https://www.iijmio.jp/"), the URL and IP address are converted by the DNS server in accordance with their correspondence.